
Incident Response Challenges : IR Evolution and Current Challenges – Part 3
Incident Response Challenges
Incident Response Evolution and Current Challenges Part 3
This is the third part of the article. To read Part 1 please click here, to read Part 2 please click here
Preventing future breaches
The last phase of an incident management plan is reporting, and avoidance of future security incidents. Therefore, a major challenge facing IR teams is to identify the exploited vulnerability and implement permanent fixes to prevent the incident from reoccurring, leading to a better-secured organization. Some of these fixes include setting up schedules for patching, security evaluations, and backups to ensure that the organization will be best placed to deal with any future security incident. Therefore, IR acts as a preventative measure for future potential attacks.
Preparing for attacks
With the increased number of attacks, organizations are challenged to adopt and increase their cyber resilience, to survive security breaches. One of the ways to ensure resilience is by having IR teams and plans that are always ready. IR teams and IR plans are two tools that are part of the larger defense mechanism that an organization develops to ensure the security or recovery of its core assets during and after a security incident. IR entails building a competent team and structuring highly effective response plans that can be activated when required. Therefore, this challenge involves planning how to ensure the defense or survival of the organization before the actual attacks begin. We’ll continue to consider this challenge with a discussion on the concept of cyber resilience in the next section.
Developing cyber resilience
Cyber resilience is a new approach to security that recognizes the threat of persistent, changing attacks. Having a resilient cybersecurity strategy that enables organizations to respond to inevitable breaches is key, rather than hoping that the data will never be compromised. As such, cyber resilience is a crucial counterpart to cybersecurity. As mentioned earlier, there are no shortcuts in cybersecurity, so it’s important to adopt a long-term strategy, as illustrated in the following figure:
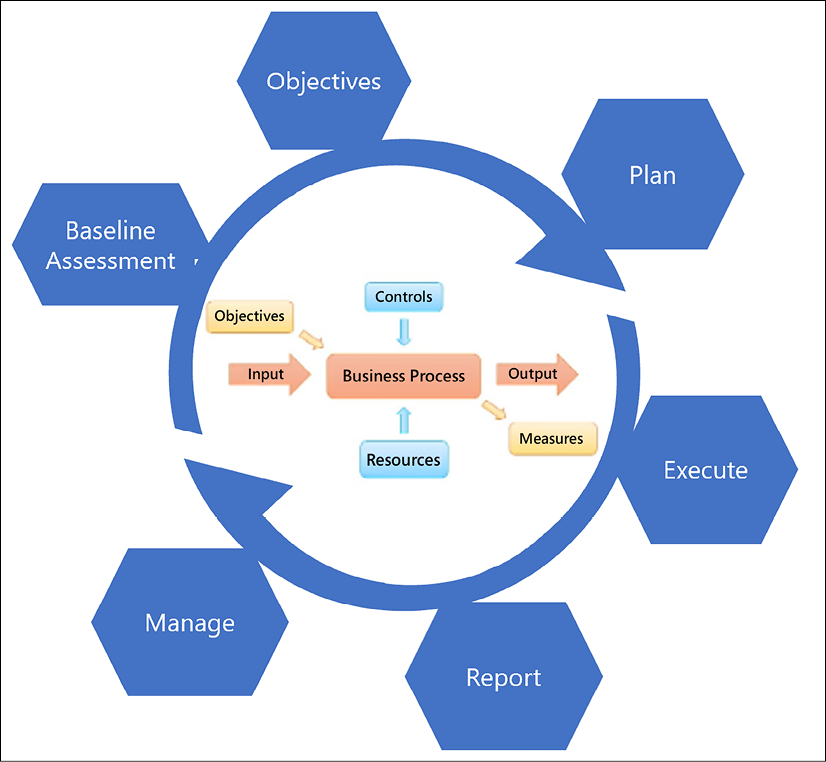
Figure 1: Cyber resilience strategy steps
The steps on how you can develop a long-term cyber resilience strategy are as follows:
- Baseline Assessment: This is the step in which you will need to align your organization’s business requirements to your operational capabilities, and determine how you can build a successful strategy.
- Objectives: In this step, you will need to identify your resources and controls to ensure that your operational objectives are fully aligned with the strategy.
- Plan: Agree on an initial plan of action, which includes working with third-party partners.
- Execute: This step is when the plan will be carried out.
- Report: Have an outcome of the strategy in the short term (30 days), mid-term (60 days), and the long term (180 days). You can change the number of outcome days based on your needs. This is based on the Objectives and Inputs, which will need to be fed into the Business Process (see the flowchart at the center of Figure 2.5), based on your organization’s Controls and Resources. These steps will help us to generate the Output (report) and Measures to take.
- Manage: Your IR plan needs to be continually updated and managed accordingly.
Now, let’s consider another challenge that faces IR teams: security safeguard assessment.
Assessing security safeguards
IR is modeled around the organization’s existing defense mechanisms. Thus, during the development of an IR plan, a challenge the organization faces is to assess all other defenses to work out a way they will work with the IR team. Commonly, network security tools, enterprise and host-based antivirus systems, endpoint detection and response systems, intrusion detection systems, cloud connections, and user awareness training are considered and evaluated when setting up an IR plan, as illustrated in Figure 2.6:
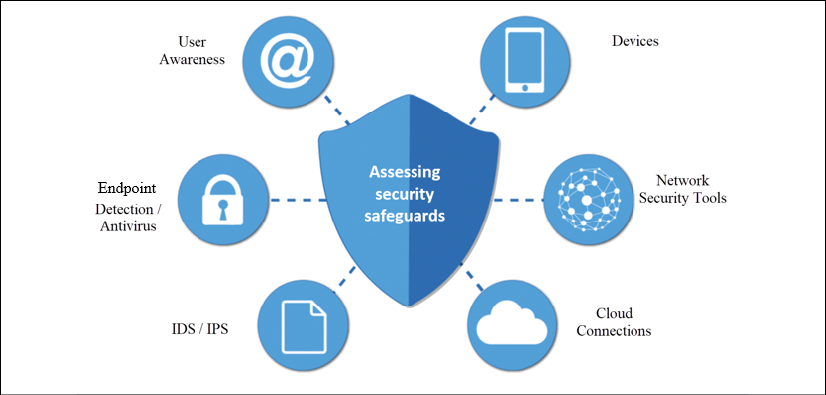
Figure 2: Assessing your security safeguards
The assessment of these tools provides room for the organization to find weaknesses in the safeguards and make changes to ensure better security.
Aiding investigations and legal prosecutions
In the IR process, the third phase is the investigation stage, where the IR team collects and examines evidence relating to the security incident. The evidence is retrieved from an assortment of sources such as logs, users, and security tools and may help identify the attacker or reveal the trails to other complacent parties. Eventually, the evidence can be used in the prosecution of suspects in court. Therefore, from a legal perspective, IR is important as it may help the organization win legal battles against suspected attackers, malicious employees, or unscrupulous third parties.
Bringing the organization together during crises
In most organizations, employees are grouped into functional units, hence they only concentrate on tasks pertinent to their departments. IR teams are composed of personnel from different departments who work toward preventing extensive damage and ensuring the recovery of the organization during security incidents. During security events such as attacks, each team member brings competencies from their respective departments. For instance, communication personnel will disseminate information as appropriate to all stakeholders during an attack, while an IT support specialist will be involved in stopping the execution of the attack. The collaboration of many departments in the IR process improves cohesion and cooperation in the organization even after the security incident has been dealt with.
Ensuring the integration of security initiatives
Organizations might have several security initiatives that work independently. For instance, many organizations have IT security policies, employee training programs, security awareness programs, IT auditing, change management plans, and penetration testing as part of their security framework. However, most of these initiatives are not integrated.
For instance, penetration testing exercises might not be connected to employee training programs. IR has a unifying effect on the existing security measures to bolster the defense capability of the organization. Therefore, during IR planning, all these tools will be identified and refined to work together to secure the organization. For example, during the planning process, related initiatives such as employee training and security awareness programs can be combined. Similarly, IT auditing and penetration testing could be made to complement each other in a situation where penetration testers identify weaknesses first, and IT auditors focus more on the problematic areas when examining the organization’s IT assets.
Improving the overall security stature of the organization
Conventionally, organizations relied on cybersecurity tools to ensure the security of their organizations. Hence, only the IT department was tasked with cybersecurity-related functions. However, as the frequency, complexity, and intensity of attacks have grown, organizations have had to adopt more effective security measures to prevent, combat, and manage attacks. IR is one of the relatively new ways to improve the security stature of the organization. When all else fails and an attack permeates to the organization, the IR team can be tasked with eliminating the source and recovering the organization. Thus, security is no longer hedged just on security software but also on a highly effective team that will resolve security threats when they occur.
The following are six best practices you can use to improve your organization’s security posture:
- Conduct a cybersecurity risk assessment
- Prioritize risk
- Track security metrics
- Implement automated cybersecurity solutions
- Educate your employees
- Create an IR plan
These categories will be explored throughout different chapters in this book.
The headings in this section have covered some of the main challenges faced by IR teams when carrying out IR. Mainly, these teams have to look at how they can secure the company’s brand, prevent future attacks, improve security stature, integrate all security initiatives, assist with evidence collection to aid in investigations, and still be a strong unit that brings the organization together during crises.
Why do we need incident response?
Incidents are on the increase and it has become apparent that if they are not contained properly, they can easily escalate into issues that can damage an organization. A reliable solution is to prepare adequately on how to address security incidents when they happen. IR enables organizations to take essential steps to address the ever-present threat of cyber threats.
Therefore, IR is a necessity in organizations today. Poor handling of incidents can lead to the escalation of manageable security events into catastrophes. As recent reports from security incidents have shown, IR helps organizations to mitigate attacks, minimize losses, and even prevent future security incidents.
To achieve the best outcomes from IR processes, the organization should ensure that it acts with speed immediately after a security event is detected. However, before executing the mitigative actions, the nature and extent of the security incident have to be determined. In the short term, the organization ought to focus on deploying resources to combat the active threat and return the organization to normalcy. This should be done in parallel with seeking assistance from law enforcement and third parties to assist with tracking down the cause. In the long term, IR activities can be focused on identifying the cause of the threat to find permanent fixes, improving the security tools used to ensure better detection and prevention, prosecuting the culpable parties, and addressing reputational damage.
Despite the reliance on conventional cybersecurity approaches that are heavily reliant on security tools, new threats can be best mitigated by people and processes. Hence, IR, which combines the efforts of security tools with people and processes, will often lead to more effective solutions. Organizations must, however, continually evaluate their IR plans and teams to ensure that their effectiveness improves over time. Nonetheless, the importance of IR in modern IT environments cannot be underestimated.
Tips
- As discussed in Chapter 1, Getting Started with Incident Response, always be ready.
- Build proper detection and reporting capabilities.
- Education/awareness should be one of your core priorities.
- Always keep an eye on data breach reports from Verizon, Microsoft, and Kaspersky, as well other vendors. If you don’t want to go through all those individual websites, you can check my blog, where all the aforementioned reports are kept under one blog post every year: https://www.ErdalOzkaya.com.
Summary
This chapter has gone through the evolution and current challenges of IR. It has explained the need for IR to respond to changes in the threat landscape and technology advancements. It has also highlighted that teams also face various challenges with IR. As explained, IR must help the organization handle incidents effectively by providing a guide to contain and mitigate the effects of security events. An IR team also has a responsibility to protect the company brand by handling any eventualities that might ruin the reputation of the company. Methods to prevent future breaches are necessary by ensuring the implementation of permanent fixes to common security incident sources and preparing for attacks by boosting cyber resilience.
Furthermore, IR contributes to the improvement of the security stature of the organization and ensures the integration of an organization’s security initiatives. Lastly, IR teams face the challenge of assisting legal investigations and court prosecutions by collecting evidence that can be used to build a case against suspects of attacks.
In the next chapter, we will look at the composition of the IR team, to learn more about the various professionals required to make the team function optimally.
Further reading
The following are resources that can be used to gain more knowledge on this chapter:
- Comodo, breach detection resources: https://www.comodo.com/business-security/email-security/breach-detection.php
- Forbes, Companies With Security Fails Don’t See Their Stocks Drop As Much: https://www.forbes.com/sites/sergeiklebnikov/2019/11/06/companies-with-security-fails-dont-see-their-stocks-drop-as-much-according-to-report/#29da9aed62e0
- Infosecurity, Companies’ Stock Value Dropped 7.5% after Data Breaches: https://www.infosecurity-magazine.com/news/companies-stock-value-dropped-1/
- DARKReading, Why Every Organization Needs an Incident Response Plan: https://www.darkreading.com/edge/theedge/why-every-organization-needs-an-incident-response-plan/b/d-id/1335395
- Infosecurity, The Importance of a Cyber Incident Response Plan and the Steps Needed to Avoid Distaster: https://www.infosecurity-magazine.com/opinions/the-importance-of-a-cyber-incident/
- NIST SP 800 https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-61r2.pdf
- IR Guideline https://security.berkeley.edu/incident-response-planning-guideline
- Binalyze
IREC
Keywords
incident response – incident response tools – what is an incident response plan -incident response methodology – incident response management – incident response procedures – incident response definition – stages of incident response – incident response services – What are the 5 steps to incident response? – Incident Response Evolution and Current Challenges – Part 3 – Incident Response Challenges -Incident Response Challenges: IR Evolution and Current Challenges – Part 3 Incident Response Challenges





