Most Prevalent Discovery Technique Free Webinar 20
Most Prevalent Discovery Technique Free Webinar 20
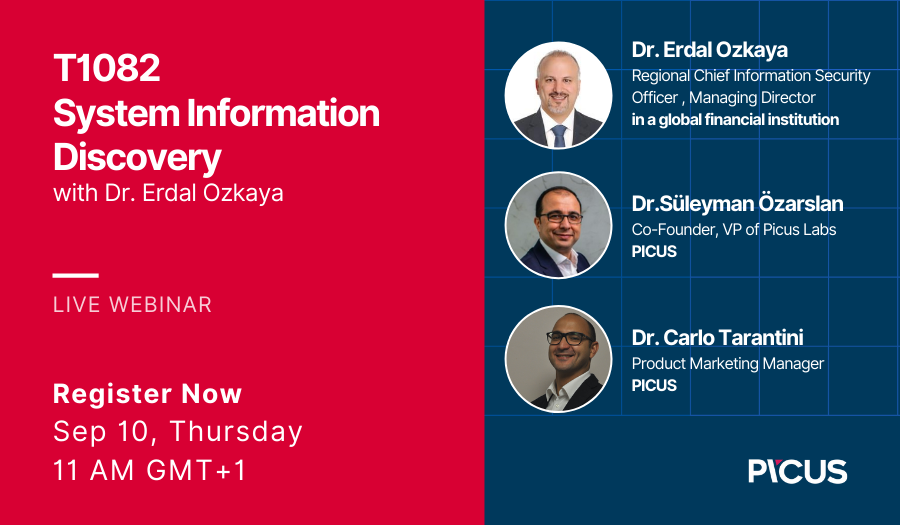
Join me with Picus Security where we will talk about t “The Most Prevalent Discovery Technique ATT&CK: T1082 System Information Discovery”
On September 10th, Dr. Erdal Ozkaya from Standard Chartered Bank will join Picus for the live webinar and we’ll talk about T1082 System Information Discovery!
- Save your seat & join us on September 10th to discover:
- How do adversaries leverage ‘System Information Discovery’ into their targets?
- What are the significant benefits that T1082 provides for adversaries?
- What are the use cases by threat actors and their malware?
- How do Red Teams simulate this technique?
- How do Blue Teams detect this technique?
- How can you test T1082 System Information Discovery with Picus in your environment?
Registration Link : https://hubs.ly/H0vMhcb0
Picus Labs, the research arm of Picus security, analyzed around 50.000 malware samples in the last year to determine TTPs used by adversaries in these malicious files. As a result of the comprehensive analysis of tens of thousands of real-world threat samples collected from numerous sources, Picus unrevealed the “Picus 10 Critical MITRE ATT&CK Techniques” to help you focus on what significantly improves your security.
Speakers
Dr. Süleyman Özarslan ,Co-Founder, VP of Picus Labs, Picus
Dr. Erdal Ozkaya, Regional Chief Information security Officer , Managing Director, Standard Chartered Bank
Dr. Carlo Tarantini , Product Marketing Manager, Picus
For more evets :
https://www.erdalozkaya.com/category/free-events/
About Picus
In 2013, Picus security pioneered Breach and Attack Simulation (BAS) technology and has helped companies improve their cyber resilience since then.
Established by cybersecurity veterans with academic backgrounds and extensive hands-on experience, Picus Security developed a transformative security Validation solution for end-to-end attack readiness visibility and effortless mitigation to pre-empt cyber attacks across all cyber defense layers.
Picus’ “The Complete security Validation Platform” provides granular and actionable insights for operational and executive teams, helps built proactive capabilities, maximizes technology utilization, and thus optimizes return on investment and keeps the risk of getting breached consistently low.