Cybersecurity Strategy for Cyber Defenders – Free VIDE0
Cybersecurity Strategy for Cyber Defenders
Hear Microsoft Cybersecurity Architect Dr Erdal Ozkaya discuss current threats and what to do with them. MC’ed by Guy Coward from IT Masters.
The webinar Agenda :
• Update on the current international cyber security threat profile
• What is Cyber Strategy and how you can build the right defense
• Erdal’s doctoral journey
• Erdal’s latest book – ‘Inside the Dark Web’
• Q&A
To watch the webinar :
To watch it i You Tube :https://www.youtube.com/watch?v=YlROT416Ps4
More about Inside the Dark Web
Inside the Dark Web provides a broad overview of emerging digital threats and computer crimes, with an emphasis on cyberstalking, hacktivism, fraud and identity theft, and attacks on critical infrastructure. The book also analyzes the online underground economy and digital currencies and cybercrime on the dark web. The book further explores how dark web crimes are conducted on the surface web in new mediums, such as the Internet of Things (IoT) and peer-to-peer file sharing systems as well as dark web forensics and mitigating techniques.
This book starts with the fundamentals of the dark web along with explaining its threat landscape. The book then introduces the Tor browser, which is used to access the dark web ecosystem. The book continues to take a deep dive into cybersecurity criminal activities in the dark net and analyzes the malpractices used to secure your system. Furthermore, the book digs deeper into the forensics of dark web, web content analysis, threat intelligence, IoT, crypto market, and cryptocurrencies. This book is a comprehensive guide for those who want to understand the dark web quickly.
After reading Inside the Dark Web, you’ll understand
- The core concepts of the dark web.
- The different theoretical and cross-disciplinary approaches of the dark web and its evolution in the context of emerging crime threats.
- The forms of cybercriminal activity through the dark web and the technological and “social engineering” methods used to undertake such crimes.
- The behavior and role of offenders and victims in the dark web and analyze and assess the impact of cybercrime and the effectiveness of their mitigating techniques on the various domains.
- How to mitigate cyberattacks happening through the dark web.
- The dark web ecosystem with cutting edge areas like IoT, forensics, and threat intelligence and so on.
- The dark web-related research and applications and up-to-date on the latest technologies and research findings in this area.
For all present and aspiring cybersecurity professionals who want to upgrade their skills by understanding the concepts of the dark web, Inside the Dark Web is their one-stop guide to understanding the dark web and building a cybersecurity plan.
Table of Contents
1. An Introduction to the Dark Web.
2. Cybercrime and the Dark Web.
3. Malicious Software.
4. Dark Web Malicious Hacker Forums.
5. Ransomware.
6. Accessing Dark Web Contents.
7. Crypto Market and Cryptocurrency.
8. Threat Intelligence from the Dark Web.
9. Social Engineering in the Dark Web.
10. Products and Vendors in Dark Web Markets.
11. Dark Web Forensics.
12. Open Source Intelligence.
13. Emerging Trend of Dark-Net and Mitigating Techniques.
14. Hands-on Dark Web.
You can order the books from :
CRC Press : https://www.crcpress.com/Inside-the-Dark-Web/Ozkaya-Islam/p/book/9780367236229
Target : https://intl.target.com/p/inside-the-dark-web-by-erdal-ozkaya-rafiqul-islam-paperback/-/A-76551768
Amazon : https://www.amazon.com/Inside-Dark-Web-Erdal-Ozkaya-ebook/dp/B07RXLHRF3/
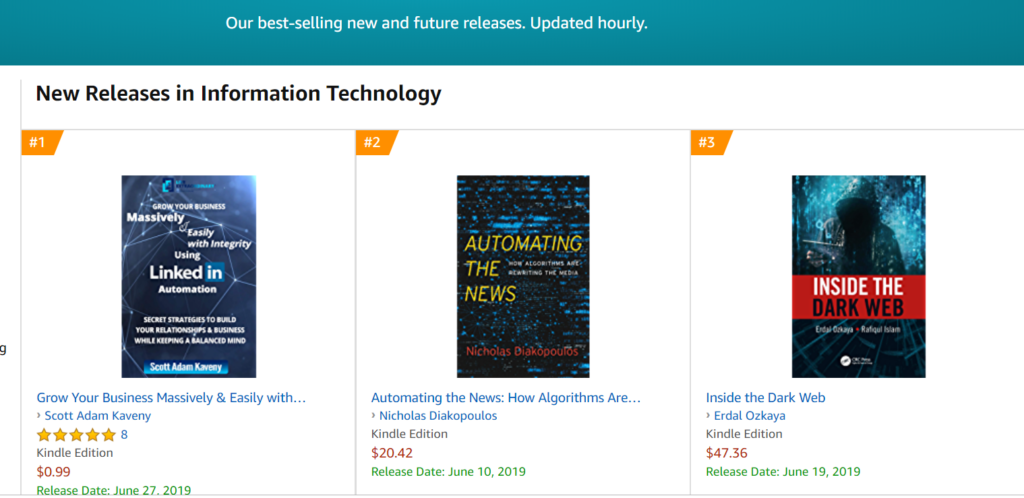
Inside The Dark Web Best Seller in Amazon
My new book “Inside The Dark Web” is number 3 in the best selling new Information Technology books at Amazon.
Thank you very much for your support, Its an awesome feeling to see your hard work gets some attention . I am looking forward to see the feedbacks.
Dr. Rafiqul and I are happy to see the results and hopefully it will continue to stay in the Best Selling lists
Thanks again
Erdal
For more info :
https://www.erdalozkaya.com/?s=inside+the+dark
Cybersecurity and Cybercrime
Introduction to Cybersecurity and Dark Web
The expansion of internet has created a great opportunity among the users in different domains, for instance, academic, government, business, and industry sectors. However, this growing development has also created the opportunity to exploit vulnerabilities to attack the infrastructure and system, conduct espionage, and wage cyberwar.
Therefore, the cyberspace needs to ensure the users are secure so that they can protect their privacy and safety in the cyber world. The term cybersecurity has been adopted by government and industry and is understood as the process by which computer networks and databases of national interest are protected, for example, large corporations and government agencies including civilian, military, and law enforcement.
https://www.erdalozkaya.com/introduction-to-cybersecurity-2/





