
Recent Evolution of the Dark Web – Great history 1960 to 2022
Recent Evolution of the Dark Web
The main pillars that have built up the dark web are security and privacy. When normal internet users feel threatened of being spied on while on the normal internet, they turn to the dark web. It has enabled spies in restrictive areas and countries where democracy is not the rule of law to continue operating without being discovered.
The dark web has also seen the creation of a suitable environment for whistle-blowers. High-profile cases have been exposed by WikiLeaks which gets some leaked information through the dark web. However, alongside all this is the main focus of the dark web which has come to be known from cybercrimes and the takedown of famous marketplaces. The following are some of the recent evolutions of the dark web.
Improved Security, Privacy, and Usability
One of the oldest dark nets is Freenet that was built in 2000 for the purpose of protecting opponents of restrictive regimes. The dark net was slow and had many usability issues. However, this was a price many were willing to pay for the type of anonymity that the dark net offered. Over time, dark nets have improved both in privacy and security. They have made it easier for any user to access them. Taking Tor, for instance, it has upgraded from using modified old versions of Firefox to newer versions.
The updated version of Tor packs has similar usability features as the latest versions of Firefox. Tor has also fixed a number of security gaps. There was a time the FBI was able to break into Tor and identify several users due to a security bug in the version of Firefox that the dark net used. Tor responded by keeping up with the newer releases of Firefox that did not have the bug. Also, Tor has been making security.
One of the most important and evolutionary improvements came about in 2017. In what was called the Alpha release, Tor was upgraded with many tweaks that fixed security weaknesses that had allowed rogue nodes to keep tabs on what was going on in a network. Rogue nodes are believed to have been used by security agencies to arrest users by identifying them in the network. In 2016, there was a zero-day vulnerability that was discovered inside Tor browsers that was identical to what the FBI was said to be using to expose Tor users.
Security Reserachers reported it as a bug that was in Firefox that could allow attackers to run any code in a targeted system thus making the target visit a malicious website that had malicious JavaScript code. The malicious page was identified to also sending hostnames, IP, and MAC addresses to 5.39.27.226. The biggest threat, however, was that the web page contained malicious JavaScript and SVG that were loaded to computers that visited it on Tor. Using this code, it was possible for an assailant (the FBI in this case) to leak details about a Tor user without leaving a digital footprint of hacking them. The JavaScript code would not download, it would just be loaded directly on a computer’s memory and execute. After the release of this zero-day vulnerability, the 5.39.27.226 was shut down, and Tor released a patch for their browser.
The following are some other vulnerabilities that are said to have allowed investigators to spy and get the identities of users:
- Window and screen size—as minute as it might seem, this was a big security challenge for Tor. It led to a warning being brandished on all Tor browsers for users not to maximize their Tor window sizes. The software would open at a default width and height, and users were warned against changing from that default size. The issue was that with the version of Tor that was being used, it was possible for JavaScript to be used to detect a Tor browser from any other browser thus making users more vulnerable as their traffic could be monitored.
- User profiling based on Mac Operating System (OS) window size—this was a unique flaw that faced Tor users that used Mac OS. When the Tor browser would launch, it would set its size as 1,000 × 1,000 px. For smaller screens, the window would be multiples of 200 and 100 px that would be ideal for the screen. There was a flaw where the Tor browser was miscalculating its window size on Mac OS leading to it occupying the height of the dock. This would make a user vulnerable since authorities could just hunt for browsers that were using window sizes of multiples of 200 px width but not 100 px height. The flaw uniquely would identify browsers accessing the Tor network and the users could then be profiled.
- Scrollbar size—Tor browsers don’t have a default size for, which helped profitable scrollbars to be added to the browsers. The area occupied by the vertical and horizontal scrollbars could, therefore, be subtracted from the window size just to find out the individual thickness of the scrollbars. The scrollbar size could be used to identify the OS and type of computer that a user was on since different OS and computers have different scrollbar sizes. It was already known that Tor on Mac OS had 15 px-thick scrollbars, while on Windows it had 17 px-thick scrollbars.
Following these and other concerns, in April 2017, the Tor Project announced that it would run on Rust code developed by the makers of Firefox. This is where Tor began to take the face of new Firefox editions. Tor was essentially relying on the secretive features of the Firefox browser. Before then, Tor used to run on C and C++ software. Tor developers said that there was a risk in continuing with C since a small mistake could be used to undermine the security of its users.
Other than Tor, the other major dark net called Freenet has also seen improvements to improve its security and performance. Freenet has been upgraded to be able to support millions of users. To preserve their anonymity, the dark net has made it possible for its users to limit the peers that can engage them. This is quite different from other dark nets that allow peers to connect to each other without restrictions. Freenet has also made it harder for outsiders to discover Freenet users and also very hard for the activity of a user on the dark net to be known. Freenet is so much sealed such that it is hard for law enforcement agencies to interfere with it.
History of Dark Web
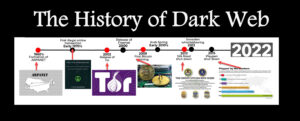
The idea of the Internet was formed in 1960 with Advanced Research Projects Agency Network, (ARPANET) as most of you do know. ARPANET was used by the US military but also Universities to have a computer-based communications system without a central core, which would protect against enemies attempting to black out entire networks by simply destroying its core during the Cold War.
History of the dark web , First Online Crime
John Markoff book “What the Dormouse Said, (Amazon link)” revealed the world’s first online crime from 70′.
“In 1971 or 1972, Stanford students using Arpanet accounts at Stanford University’s Artificial Intelligence Laboratory engaged in a commercial transaction with their counterparts at Massachussetts Institute of Technology. Before Amazon, before eBay, the seminal act of e-commerce was a drug deal. The students used the network to quietly arrange the sale of an undetermined amount of marijuana.”
1990: Release of Public Internet
32 years ago (August 1991) the internet became public, and sharing “copy righted” music, documents became common with it, which was and still is “illegal”
The First TOR – 2002
The most important Dark Web development of all time happened in 2002, with the release of TOR or The Onion Router , which is known for being a private internet browser was released to help people browse the internet freely, anonymously without leaving any “tracks” behind, while the intentions was good the outcome was not perfect as Tor become quickly a place where criminals started to do business as Tor was against censorship
2008: Tor Becomes User Friendly
The platform developed was overly complex and it had many technical restrictions and accessibility issues, which forced developers to make the platform more user friendly
2009: Birth of Bitcoin
As many illegal transactions started to take place, it was hard to keep the “anonymous ” goal in teh Dark Web. The answer for this was inventing “cryptocurrency” as Bank Transfers or PayPal transactions was not “private” as customers could potentially exposed. Out of many cryptocurrencies Bitcoin became the most popular, Bitcoin solved the problem that previous versions of cryptocurrency couldn’t (more info)
Of course, Eiter Dark WEb nor Bitcoin is not just used illegally.
The Arab Spring (2010)
The Dark Web was not just there for anonymous browsing, being anonymous gave many people the opportunity to get together and unite as activists, especially in countries where “free speech ” is not welcome. The Tor browser not only protected people’s identities online, but also allowed them to access critical resources, social media, and blocked websites, which played a major effect of Arab Spring
2013: Silk Road Shutdown
The Silk Road made buying and selling illegal drugs as easy as buying used electronics, which took FBI’s attention and they shut it down.
2013: Snowden Whistleblowing
I am sure you know who Edward Snowden is, if not you can read more about it here: Edward was an NSA employee, who leaked highly classified information about NSA on how they are doing mass surveillance. Snowden used Tor when the known internet companies deleted the NSA documents forced by law.
2015: Playpen Shutdown
In my opinion this was the best shutdown of Dark Web. Playpen, was a widely used dark website for the distribution of child pornography where FBI was able again to successfully shutdown the web site.
The Dark Web is not a bad place , infact it has some bad use for sure like the Silkroad and Playpen examples. As long as you are aware and use it with caution You should be fine there!
Part 2 of this article will include:
-
Improvements in User Interface Design
-
Trust-Based Markets
-
Continuity
-
Crime Patterns
To read more Cybersecurity related articles, click here:
Inside the Dark Web
Inside the Dark Web provides a broad overview of emerging digital threats and computer crimes, with an emphasis on cyberstalking, hacktivism, fraud and identity theft, and attacks on critical infrastructure. The book also analyzes the online underground economy and digital currencies and cybercrime on the dark web. The book further explores how dark web crimes are conducted on the surface web in new mediums, such as the Internet of Things (IoT) and peer-to-peer file sharing systems as well as dark web forensics and mitigating techniques.
This book starts with the fundamentals of the dark web along with explaining its threat landscape. The book then introduces the Tor browser, which is used to access the dark web ecosystem. The book continues to take a deep dive into cybersecurity criminal activities in the dark net and analyzes the malpractices used to secure your system. Furthermore, the book digs deeper into the forensics of dark web, web content analysis, threat intelligence, IoT, crypto market, and cryptocurrencies. This book is a comprehensive guide for those who want to understand the dark web quickly.
After reading Inside the Dark Web, you’ll understand
- The core concepts of the dark web.
- The different theoretical and cross-disciplinary approaches of the dark web and its evolution in the context of emerging crime threats.
- The forms of cybercriminal activity through the dark web and the technological and “social engineering” methods used to undertake such crimes.
- The behavior and role of offenders and victims in the dark web and analyze and assess the impact of cybercrime and the effectiveness of their mitigating techniques on the various domains.
- How to mitigate cyberattacks happening through the dark web.
- The dark web ecosystem with cutting edge areas like IoT, forensics, and threat intelligence and so on.
- The dark web-related research and applications and up-to-date on the latest technologies and research findings in this area.
For all present and aspiring cybersecurity professionals who want to upgrade their skills by understanding the concepts of the dark web, Inside the Dark Web is their one-stop guide to understanding the dark web and building a cybersecurity plan.
You can order the books from :
CRC Press : https://www.crcpress.com/Inside-the-Dark-Web/Ozkaya-Islam/p/book/9780367236229
Target : https://intl.target.com/p/inside-the-dark-web-by-erdal-ozkaya-rafiqul-islam-paperback/-/A-76551768
Amazon : https://www.amazon.com/Inside-Dark-Web-Erdal-Ozkaya-ebook/dp/B07RXLHRF3/
More info about my other books
Sponsor:
To stay safe in the dark web or on the internet use Xcitium, Today’s cyber warfare has proven no vendor can detect zero-day malware from reaching your network and endpoints, but our patented technology specializes in preventing any damage.
Keywords:
History of the dark web, Birth of Bitcoin , history of the dark web, history of dark web , Recent Evolution of the Dark Web – Great history 1960 to 2022





