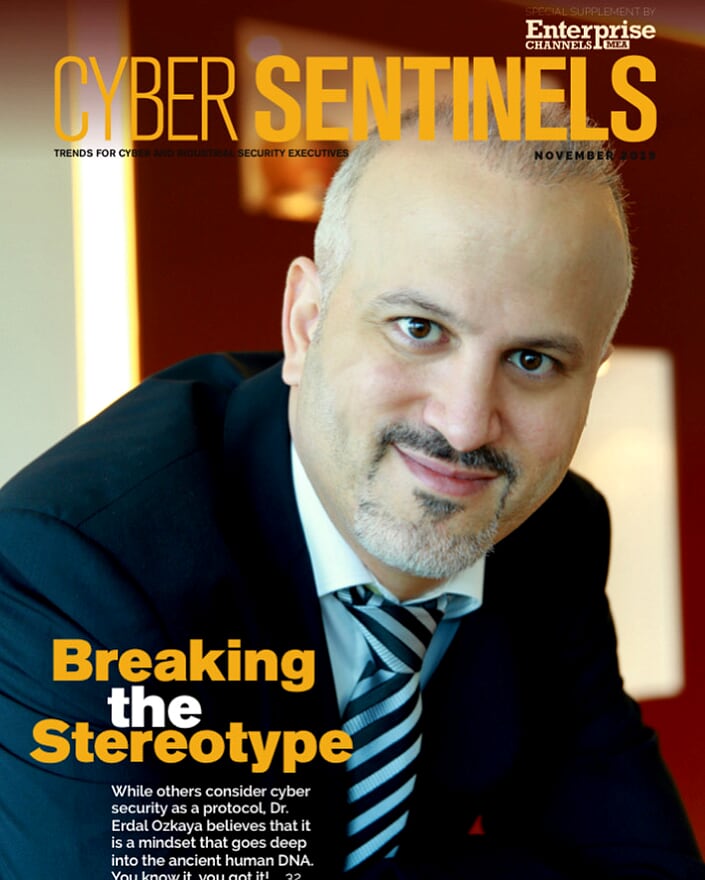
Breaking the Stereotype
Breaking the Stereotype
Whilst others consider cyber security as a protocol, Dr. Erdal Ozkaya believes that it is a mindset that goes deep into the ancient human DNA. You know it, you got it!
By : Anushree Dixit via Cyber Sentinels Magazine
Dr. Erdal Ozkaya’s association with IT goes back to an era in 1996 when computers were not only rare, but expensive as well. Security in those days was limited to formatting Windows with various floppy disks.
With affiliations to various geographies like Turkey, Germany, Australia and now UAE, Dr. Erdal has tried and tested human behavior and its core DNA in security like none other.
WEAKNESS- CURIOSITY
“Regardless of which country you are in or which nationality you belong to, human behavior is the same,” says Dr. Erdal.
“Let me give you a very ancient and well-known citation to this theory of mine. Adam and Eve (different name in different culture) were thrown out of the paradise for just one reason— eating the forbidden fruit. Even though they had a garden full of fruits to devour, they were tempted by the forbidden fruit and were curious to taste it, because they were told ‘NOT TO TOUCH’.”
While listening to this, my mind automatically draws in analogies and allegories from various mythological instances. The famous ‘Lakshman Rekha’ from Ramayan’s Sita Haran chapter also tells us that the solution or the ‘lakshman rekha’ had no technical flaws, but it was the concerned heart of Sita that forced her to cross the line, leading to the demon king Ravana kidnapping her.
The Trojan horse; how can someone believe that the enemy withdrew their forces leaving a gift? The curious nature of the Troy soldiers led to the diminish of a nation.
Dr. Erdal believes that the very nature of human being and the curious DNA is the sole reason for a majority of breaches that happen.
“In order to weave a successful cybersecurity strategy, we have to understand that, it all starts with humans. Let us imagine that we invented a time machine, travelled ahead 50 years, took the latest technology from there and came back to 2019.Will that make us secure?…. No, because the human factor still exists.”
WEAKNESS – IGNORANCE
Well, Ignorance is never a bliss, if you ask Dr. Erdal.
“The practice of ignoring alerts is the second point of weakness that we see in the human beings. In a situation where I have a personal situation to attend, I will tend to ignore an email that just landed in my inbox. It may look suspicious to me, but I will choose to ignore and look at it later.”
WEAKNESS – UNDERESTIMATING
Dr. Erdal pulls out a bit from a book written in the 5th Century BC, named ‘The Art of War’. “It is a very ancient book, but the facts still stand true. In the book, the writer, Sun Tzu says that, in order to win a battle you not only need to know yourself but know the enemy as well. The more you know the enemy, the more you own the battleground.”
WEAKNESS – EXPERTISE
Buying technology, understanding technology, using technology. According to Dr. Erdal, these three are fairly different terms.
“I will give my grandmother a Bugatti car and give Michael Schumacher a Hyundai. Who do you think will win if they race? Of course Schumacher, we know! Because it is not about having the fanciest of cars, but knowing how to drive one. Similarly, organizations should realize that it is not about having the most expensive technologies in place, but knowing which technologies fits where and how to implement it in the organizational architecture.”
THE ART OF CHOOSING THE RIGHT VENDOR
‘Not all vendors fit, not all vendors are misfit.’
“My suggestion to my colleague CISOs and security heads is that, choose the right vendor. Believe me, it is not as difficult as it appears. Know who you are, know what you need and do not let the vendor tell you what you need. It has to come from you. Be vocal about your problems and let the vendor give you the solution. We, as the CISOs or head of security often do not want to bring into limelight the vulnerabilities or the gaps that we have in our organization, but I would strongly recommend that we do. No solutions are bad, it is only about what fits your company the best. Go for that!”
According to Dr. Erdal, Cyber security is like green tea and coffee. Our bodies respond to both differently and choice varies from person to person. If you have a clear understanding of the technology brought in by the solution provider, you will achieve the desired result.
“My role with Standard Chartered Bank also revolves around this – understand what the bank wants, work together with the teams and meet as many people as possible and reach out to friends.” he adds.
POST BREACH SCENARIOS
It is a regular affair to see innumerable posts, advices and comments pouring in from the industry after a threat happens.
Dr. Erdal says that there are two types of organizations; one that know they are being hacked and other that do not know. But the fact is that, in both cases you are hacked. “When a football match is happening, it is very easy to sit in front of a TV and judge a player and remark that he should have done this or that to score a goal. Similarly, in the industry, once a breach happens we have various inputs coming in stating what should have been done.
Instead, the question that should be asked is, why did it happen. I would also recommend my partners and colleagues in the region to share information and not keep it to themselves. Many times it happens that a breach happens and the information shared in a media or press release is that everything is under control. This should not be the case. The more we share, the more we learn. We should all imbibe this culture of taking security as a shared responsibility.
I have worked in different companies, some cases it was an insider who leaked information and some with a vulnerability that they could not fix. Every car has a bumper and bumpers are made to protect the engines in small accidents.
‘BANK’ing ON TECHNOLOGY
Before joining Standard Chartered Bank, Dr. Erdal was asked about his knowledge on banking. He says with a smile, “I told them, I do not have to understand banking, I have to understand the technology behind it. There is no bank today that runs without a sound technology framework. One thing that I was hooked on to was the willingness of Standard Chartered Bank to be world class in cyber-security and I am here to contribute to that.
If you analyze the various threats and breaches that have happened, Standard Chartered will not surface in that list. If I speak on behalf of the sector as well, I can proudly say that the banks in this region have hired and retained the right talent and professionals to run their security framework smoothly.”
classic stereotypes
Cyber Sentinel Dr Erdal OzkayaWe all know the classic stereotypes – women in the kitchen, men in the office, cybersecurity as a male-only domain. But Dr. Erdal Ozkaya is breaking down these preconceived notions with his pioneering research into the numerous ways cyber security is a mindset that taps into our ancient human DNA. With groundbreaking insights into this emerging field, Dr. Ozkaya is helping to redefine the future of cyber security.
Through his work, he is debunking the myths that have long been perpetuated about the field, and demonstrating the incredible potential of the power of human minds to protect our data. With new approaches to the development of cyber security, Dr. Ozkaya is revolutionizing the way we think about protecting ourselves from cyber threats.
So, if you’re looking to break down the walls of preconceived notions and make your mark on the world of cyber security, join Dr. Ozkaya on his journey to redefine the way we think about cyber security.
Download the Magazine here
About Cyber Sentinels , click here
Erdal in the news , click here
Cyber Sentinels






