CBK Suggested References – Great resources suggested by (ISC)²
CBK Suggested References
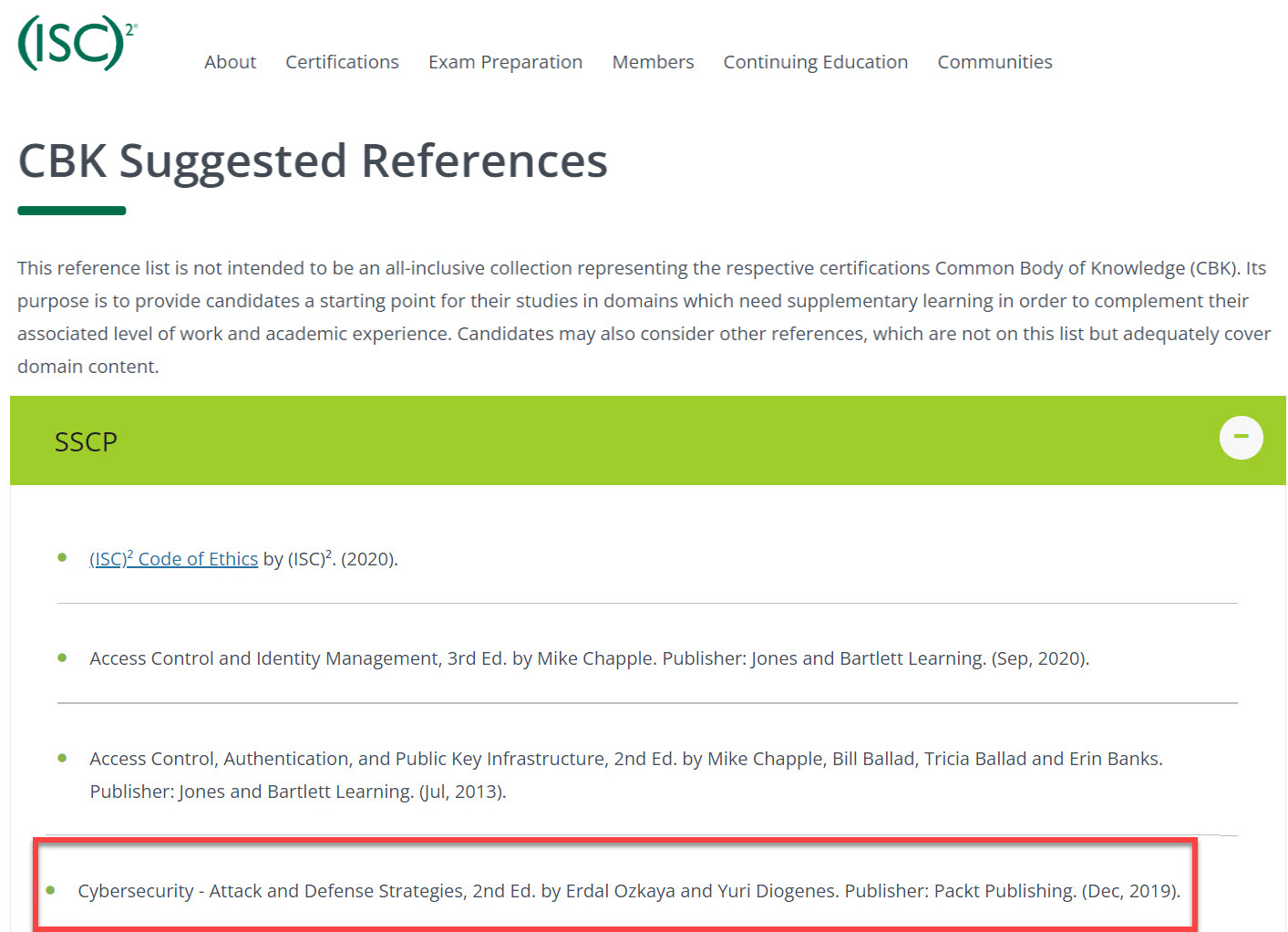
Did you know that our book, Cybersecurity Attack and Defense Strategies is listed in one of the World’s Most Prestigious certification bodies as a Reference book?
This reference list is not intended to be an all-inclusive collection representing the respective certifications Common Body of Knowledge (CBK). Its purpose is to provide candidates a starting point for their studies in domains which need supplementary learning in order to complement their associated level of work and academic experience. Candidates may also consider other references, which are not on this list but adequately cover domain content.
Note: (ISC)² does not endorse any particular text or author and does not imply that any or all references be acquired or consulted. (ISC)² does not imply nor guarantee that the study of these references will result in an examination pass.
- SC)² Code of Ethics by (ISC)². (2020).
- Access Control and Identity Management, 3rd Ed. by Mike Chapple. Publisher: Jones and Bartlett Learning. (Sep, 2020).
- Access Control, Authentication, and Public Key Infrastructure, 2nd Ed. by Mike Chapple, Bill Ballad, Tricia Ballad and Erin Banks. Publisher: Jones and Bartlett Learning. (Jul, 2013).
- Applied Cryptography: Protocols, Algorithms and Source Code in C, 20th Anniversary Ed. by Bruce Schneier. Publisher: Wiley. (Mar, 2015).
- Building an Information Security Awareness Program, 1st Ed. by Bill Gardner and Valerie Thomas. Publisher: Syngress. (Aug, 2014).
- Business Continuity and Disaster Recovery Planning for IT Professionals, 2nd Ed. by Susan Snedaker. Publisher: Syngress. (Sep, 2013).
- Cisco ASA: All-in-One Next Generation Firewall, IPS, and VPN Services 3rd Ed. by Jazib Frahim and Omar Santos. Publisher: Cisco Press. (Apr, 2014).
- Computer and Information Security Handbook, 3rd Ed. by John Vacca. Publisher: Morgan Kaufmann. (May, 2017).
- Computer Security Fundamentals, 4th Ed. by Chuck Easttom. Publisher: Pearson IT Certification. (Oct, 2019).
- Cryptography and Network Security Principles and Practice, 6th Ed. by William Stallings. Publisher: Pearson. (Mar, 2013).
- Cryptography InfoSec Pro Guide by Sean-Philip Oriyano. Publisher McGraw-Hill. (Aug, 2013).
- Cybersecurity – Attack and Defense Strategies, 2nd Ed. by Erdal Ozkaya and Yuri Diogenes. Publisher: Packt Publishing. (Dec, 2019).
- Cybersecurity Incident Response: How to Contain, Eradicate, and Recover from Incidents by Eric C. Thompson. Publisher: Apress. (Sep, 2018).
- Digital Forensics and Incident Response, 2nd Ed. by Gerard Johansen. Publisher: Packt Publishing. (Jan, 2020).
- Fundamentals of Information Systems Security, 4th Ed. by David Kim, Michael G. Solomon. Publisher: Jones & Bartlett Publishers. (Nov, 2021).
- Identity and Access Management: Business Performance Through Connected Intelligence, 1st Ed. by Ertem Osmanoglu. Publisher: Syngress. (Nov, 2013).
- Network Defense and Countermeasures: Principles and Practices, 3rd Ed. by Chuck Easttom. Publisher: Pearson IT Certification (Apr, 2018).
https://www.isc2.org/Certifications/References#
About Cybersecurity – Attack and Defense Strategies
Cybersecurity – Attack and Defense Strategies, Second Edition is a completely revised new edition of the bestselling book, covering the very latest security threats and defense mechanisms including a detailed overview of Cloud Security Posture Management (CSPM) and an assessment of the current threat landscape, with additional focus on new IoT threats and cryptomining.
Cybersecurity starts with the basics that organizations need to know to maintain a secure posture against outside threat and design a robust cybersecurity program. It takes you into the mindset of a Threat Actor to help you better understand the motivation and the steps of performing an actual attack – the Cybersecurity kill chain. You will gain hands-on experience in implementing cybersecurity using new techniques in reconnaissance and chasing a user’s identity that will enable you to discover how a system is compromised, and identify and then exploit the vulnerabilities in your own system.
This book also focuses on defense strategies to enhance the security of a system. You will also discover in-depth tools, including Azure Sentinel, to ensure there are security controls in each network layer, and how to carry out the recovery process of a compromised system.
What you will learn
- The importance of having a solid foundation for your security posture
- Use cyber security kill chain to understand the attack strategy
- Boost your organization’s cyber resilience by improving your security policies, hardening your network, implementing active sensors, and leveraging threat intelligence
- Utilize the latest defense tools, including Azure Sentinel and Zero Trust Network strategy
- Identify different types of cyberattacks, such as SQL injection, malware and social engineering threats such as phishing emails
- Perform an incident investigation using Azure Security Center and Azure Sentinel
- Get an in-depth understanding of the disaster recovery process
- Understand how to consistently monitor security and implement a vulnerability management strategy for on-premises and hybrid cloud
- Learn how to perform log analysis using the cloud to identify suspicious activities, including logs from Amazon Web Services and Azure
Book Reviews
Review by Government Technology :
Review by HelpNet Security :
https://www.helpnetsecurity.com/2020/04/22/review-cybersecurity-attack-and-defense-strategies/
Some of the Award of the Book:
Cybercrime Magazine
https://www.helpnetsecurity.com/2020/04/22/review-cybersecurity-attack-and-defense-strategies/
Read This Twice:
https://www.readthistwice.com/lists/best-cybersecurity-books
Who This Book Is For
For the IT professional venturing into the IT security domain, IT pentesters, security consultants, or those looking to perform ethical hacking. Prior knowledge of penetration testing is beneficial.
To see my other books:
https://www.erdalozkaya.com/about-erdal-ozkaya/my-books/
About : (ISC)²: The World’s Leading Cybersecurity Professional Organization
You face immense pressure to stay ahead of attacks and up-to-date in our ever-changing security profession. But you aren’t alone.
(ISC)² is an international, nonprofit membership association for information security leaders like you. We’re committed to helping our members learn, grow and thrive. More than 158,000 certified members strong, we empower professionals who touch every aspect of information security.
How can we help you make an impact in your career and advance our industry? Through our globally recognized certifications. Our vast networking and collaboration opportunities. Our Professional Development Institute and leadership tools.
We’re also committed to educating the general public through our support of The Center for Cyber Safety and Education. Because we get it. Protecting information is everyone’s job — not just IT’s job!
Join us in our vision of inspiring a safe and secure cyber world.
History Of (ISC)²
(ISC)² was founded in 1989 as the International Information System Security Certification Consortium, Inc. Our founders saw the need for standardization and certification in the cybersecurity industry. Since then, our founders and members have been shaping the information security profession.
Are you ready to make your mark?
Distinguish Yourself With Globally-Recognized Certifications
(ISC)² information security certifications are recognized as the global standard for excellence. They allow you to prove your expertise and highlight your skill mastery. And for employers, having certified employees means your organization is better prepared to protect your critical information assets and infrastructures.
(ISC)² created and maintains the Common Body of Knowledge (CBK) on which the certifications are based. The CBK defines global industry standards and best practices in information security.
Certification Programs
You work in a world where you always have to stay one step ahead. So do we. We were honored to be the first information security certifying body to meet the requirements of ANSI/ISO/IEC Standard 17024. (This is a global benchmark for certifying people.)
All of our certifications have been accredited against this standard.
ISC CBK Suggested References =





