
ICS CBK Suggested References – (ISC)2
ICS CBK Suggested References
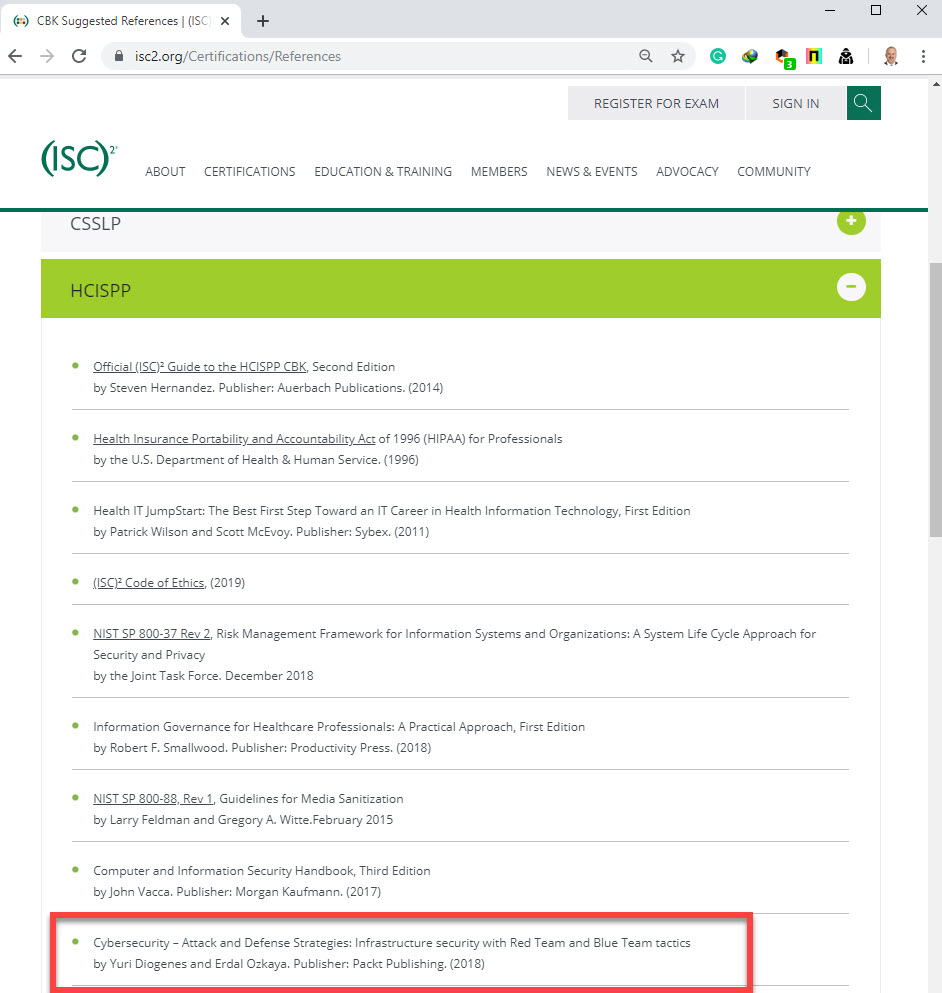
Did you know that our book, Cybersecurity Attack and Defense Strategies is listed in one of the World’s Most Prestigious certification bodies as a Reference book?
This reference list is not intended to be an all-inclusive collection representing the respective certifications Common Body of Knowledge (CBK). Its purpose is to provide candidates a starting point for their studies in domains which need supplementary learning in order to complement their associated level of work and academic experience. Candidates may also consider other references, which are not on this list but adequately cover domain content.
Note: (ISC)² does not endorse any particular text or author and does not imply that any or all references be acquired or consulted. (ISC)² does not imply nor guarantee that the study of these references will result in an examination pass.
CBK Suggested References
This reference list is not intended to be an all-inclusive collection representing the respective certifications Common Body of Knowledge (CBK). Its purpose is to provide candidates a starting point for their studies in domains which need supplementary learning in order to complement their associated level of work and academic experience. Candidates may also consider other references, which are not on this list but adequately cover domain content.
Note: (ISC)² does not endorse any particular text or author and does not imply that any or all references be acquired or consulted. (ISC)² does not imply nor guarantee that the study of these references will result in an examination pass.
About : (ISC)²: The World’s Leading Cybersecurity Professional Organization
You face immense pressure to stay ahead of attacks and up-to-date in our ever-changing security profession. But you aren’t alone.
(ISC)² is an international, nonprofit membership association for information security leaders like you. We’re committed to helping our members learn, grow and thrive. More than 158,000 certified members strong, we empower professionals who touch every aspect of information security.
How can we help you make an impact in your career and advance our industry? Through our globally recognized certifications. Our vast networking and collaboration opportunities. Our Professional Development Institute and leadership tools.
We’re also committed to educating the general public through our support of The Center for Cyber Safety and Education. Because we get it. Protecting information is everyone’s job — not just IT’s job!
Join us in our vision of inspiring a safe and secure cyber world.
History Of (ISC)²
(ISC)² was founded in 1989 as the International Information System Security Certification Consortium, Inc. Our founders saw the need for standardization and certification in the cybersecurity industry. Since then, our founders and members have been shaping the information security profession.
Are you ready to make your mark?
Distinguish Yourself With Globally-Recognized Certifications
(ISC)² information security certifications are recognized as the global standard for excellence. They allow you to prove your expertise and highlight your skill mastery. And for employers, having certified employees means your organization is better prepared to protect your critical information assets and infrastructures.
(ISC)² created and maintains the Common Body of Knowledge (CBK) on which the certifications are based. The CBK defines global industry standards and best practices in information security.
Certification Programs

You work in a world where you always have to stay one step ahead. So do we. We were honored to be the first information security certifying body to meet the requirements of ANSI/ISO/IEC Standard 17024. (This is a global benchmark for certifying people.)
All of our certifications have been accredited against this standard.





