This post will take you through Structured Threat Information Expression (STIX), Trusted Automated Exchange of Intelligence Information (TAXII), Oasis Open Command and Control (OpenC2), Traffic Light Protocol (TLP), and Cyberanalytics Repository by MITRE (CAR). With the knowledge of the aforementioned resources, you will be better equipped to identify threats and vulnerabilities.
Practical Cyber Threat Intelligence Gather, Process, and Analyze Threat Actor Motives, Targets, and Attacks with Cyber Intelligence Practices Easy to pronounce, write , say I am proud to announce my sixteenth book , which is called “Practical Cyber Threat Intelligence” and will be very soon released via BPB Publishing. I wanted to share this news […]
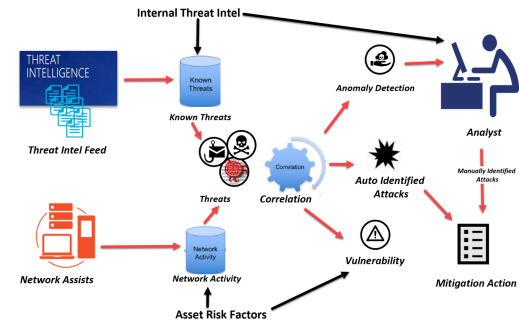
Cyber threat intelligence is information about a prevailing or evolving cyber threat that can be disseminated by threat intelligence partners to organizations in order to
reinforce security against cyber-attack vectors , This short article will help you to leant how to build a Cyber Threat Intelligence Platform in 5 steps