The Cloud Roadshow – Kuwait 2022 edition – join for free
The Cloud Roadshow
The Kuwait edition of the cloud roadshow 2022 series is designed to allow for a meaningful exchange of insights with local technology and cloud stakeholders and to ultimately contribute to the national cloud maturity levels in Kuwait. The outcome of each round table will be summarized, analyzed and published in an Opinion Piece for public consumption as a foundation to tackle country-specific pain points and to keep this exercise open for future iterations of the initiative.

When: October 26
Registration: Click Here
Cloud security defined
Cloud security is a discipline of cybersecurity that focuses on protecting cloud systems and data from internal and external threats, including best practices, policies, and technologies that help companies prevent unauthorized access and data leaks. When developing a cloud security strategy, companies must take into account four types of cloud computing environments:
Public cloud environments
Are run by cloud service providers. In this environment servers are shared by multiple tenants.
Private cloud environments
Can be in a customer-owned data center or run by a public cloud service provider. In both instances, servers are single tenant, and organizations don’t have to share space with other companies.
Hybrid cloud environments
Are a combination of on-premises data centers and third-party clouds.
Multicloud environments
Include two or more cloud services operated by different cloud service providers.
Why is cloud security important?
The cloud has become an integral part of online life. It makes digital communication and work more convenient and has spurred rapid innovation for organizations. But when friends share photographs, coworkers collaborate on a new product, or governments deliver online services, it’s not always clear where the data itself is being stored. People may inadvertently move data to a less secure location, and with everything internet accessible, assets are at greater risk of unauthorized access.
Data privacy is also increasingly important to people and governments. Regulations like the General Data Protection Regulation (GDPR) and Health Insurance Portability and Accountability Act (HIPAA) require organizations that collect information to do so transparently and put in place policies that help prevent data from being stolen or misused. Failure to comply can result in expensive fines and reputational harm.
To remain competitive, organizations must continue to use the cloud to iterate rapidly and make it easy for employees and customers to access services, while protecting data and systems from the following threats:
- Compromised accounts: Attackers often use phishing campaigns to steal employee passwords and gain access to systems and valuable corporate assets.
- Hardware and software vulnerabilities: Whether an organization uses a public or private cloud, it’s critical that the hardware and software is patched and up to date.
- Internal threats: Human error is a big driver of security breaches. Misconfigurations can create openings for bad actors, and employees often click on bad links or inadvertently move data to locations with less security.
No matter which type of environment or combination of environments an organization uses, cloud security is intended to protect physical networks, including routers and electrical systems, data, data storage, data servers, applications, software, operating systems, and hardware.
How does cloud security work?
Cloud security is a shared responsibility between cloud service providers and their customers. Accountability varies depending on the type of services offered:
Infrastructure as a service
In this model, cloud service providers offer computing, network, and storage resources on demand. The provider is responsible for securing the core computing services. Customers must secure everything on top of the operating system including applications, data, runtimes, middleware, and the operating system itself.
Platform as a service
Many providers also offer a complete development and deployment environment in the cloud. They take responsibility for protecting the runtime, middleware, and operating system in addition to the core computing services. Customers must safeguard their applications, data, user access, end-user devices, and end-user networks.
Software as a service
Organizations can also access software on a pay-as-you go model, such as Microsoft Office 365 or Google Drive. In this model, customers still need to provide security for their data, users, and devices.
No matter who’s responsible, there’re four primary aspects to cloud security:
- Limiting access: Because the cloud makes everything internet accessible, it’s incredibly important to ensure that only the right people have access to the right tools for the right amount of time.
- Protecting data: Organizations need to understand where their data is located and put the appropriate controls in place to safeguard both the data itself and the infrastructure where the data is hosted.
- Data recovery: A good backup solution and data recovery plan is critical in case there’s a breach.
- Response plan: When an organization is attacked, they need a plan to reduce the impact and prevent other systems from becoming compromised.
Types of cloud security tools
Cloud security tools address vulnerabilities from both employees and external threats. They also help mitigate errors that occur during development and reduce the risk that unauthorized people will gain access to sensitive data.
Cloud security posture management
Cloud misconfigurations happen frequently and create opportunities for compromise. Many of these errors occur because people don’t understand that the customer is responsible for configuring the cloud and securing applications. It’s also easy to make a mistake in big corporations with complex environments.
A cloud security posture management solution helps reduce risk by continuously looking for configuration errors that could lead to a breach. By automating the process, these solutions reduce the risk of mistakes in manual processes and increase visibility into environments with thousands of services and accounts. Once vulnerabilities are detected, developers can correct the issue with guided recommendations. Cloud security posture management also continuously monitors the environment for malicious activity or unauthorized access.
Cloud workload protection platform
As organizations have instituted processes that help developers build and deploy features faster, there’s a greater risk that security checks will be missed during development. A cloud workload protection platform helps secure the computing, storage, and networking capabilities needed by applications in the cloud. It works by identifying workloads in public, private, and hybrid cloud environments and scanning them for vulnerabilities. If vulnerabilities are discovered the solution will suggest controls to fix them.
Cloud access security broker
Because it’s so easy to find and access cloud services, it can be difficult for IT to keep on top of all the software used in the organization.
Cloud access security brokers (CASB) help IT gain visibility into cloud app usage and provide a risk assessment of each app. These solutions also help protect data and meet compliance goals with tools that show how data is moving through the cloud. Organizations also use these tools to detect unusual user behavior and remediate threats.
Identity and access
Controlling who has access to resources is critical to protecting data in the cloud. Organizations must be able to ensure that employees, contractors, and business partners all have the right access whether they are onsite or working remotely.
Organizations use identity and access solutions to verify identities, limit access to sensitive resources, and enforce multifactor authentication and least privilege policies.
Cloud infrastructure entitlement management
Identity and access management gets even more complicated when people access data across multiple clouds. A cloud infrastructure entitlement management solution helps a company gain visibility into which identities are accessing which resources across their cloud platforms. IT teams also use these products to apply least privilege access and other security policies.
(Source : Microsoft)
Agenda
- Welcome address by Dr. Ammar Alhusaini from the Central Agency for Information Technology (CAIT)
- Welcome message from MENA Cloud AllianceThe Middle East and North Africa Cloud Alliance (MENACA) are the only home-grown, vendor-agnostic industry Association focused on monitoring, identifying and resolving issues around cloud adoption in the MENA region. MENACA strives to give the industry a unique voice and to provide a wide range of stakeholders with unbiased insights into the region’s cloud ecosystem. Our founding members include global as well as regional leading technology thought-leaders with a vested interest in creating a dialogue around cloud computing and its impact on MENA’s digital economies
-
Roundtable: Cloud regulatory landscape
- Roundtable: Connecting to the cloud: Pain points, recommendations, and alternatives
- Roundtable: Governments – Digital transformation and cloud
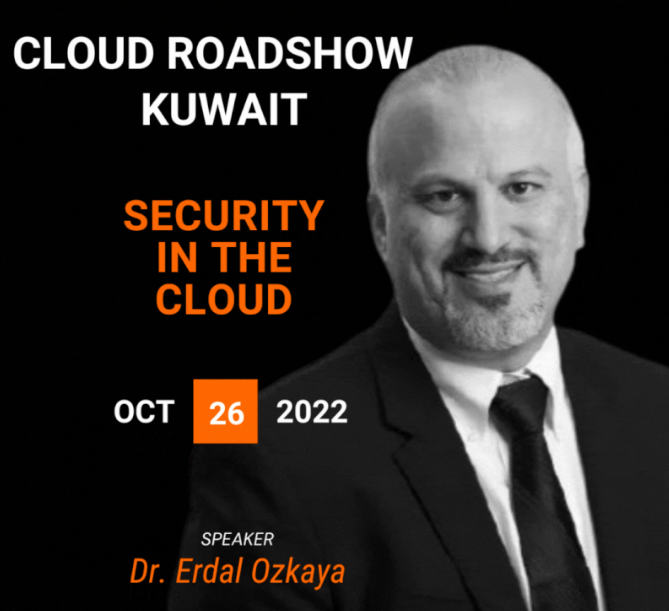
- Roundtable: Security in the cloud
Ahmed Abdel Hamid Amazon Web Services
Omid Mahboubi MENA Cloud Alliance
Dr Erdal Ozkaya – XCITIUM
Shaheela Banu Kuwait Gulf Oil Company
7. Workshop: Tech-agnostic Cloud audit
8. Workshop: CLOUD Act – Facts Vs. myths
Speakers
Omid Mahboubi
Yasmine Afifi
Dr. Omer Dawelbeit
Ahmed Abdel Hamid
Mohamed Afifi
Jaco Fourie
Sandor Fulop
Carl Roberts
Roland Abi Najem
Kassem Issa
Don O’Shaughnessy
Wasim Parkar
Dr. Erdal Ozkaya
Sathya Andivel
Shaheela Banu
Grant Holmes
.
Dr. Erdal Ozkaya Xcitium Roland Abi Najem Andrew Grenville Orixcom Mohamed Afifi Ahmed Abdel Hamid Dr. Omer Dawelbeit
Yasmine Afifi Amazon Web Services (AWS)Carl Roberts Oxford Brookes University shaheela Banu Kassem Issa Diyar United Company Wasim Parkar Jaco Fourie Temenos Don O’Shaughnessy Sathya Andivel, CMA, PMP, PgMP, CSSBB, TOGAF Hesabe Company for Electronic Payments and Settlements
.
#MENAcloudallince #cloud #roadshow #kuwait
#cloudsecurity #cloudcomputing #cloudmigration #cloudarchitect #cloudinfrastructure #cloudregulation #cloudadoption #AI #ML #bigdata #conectivity #telecom #cloudprovider #clouduser The Cloud Roadshow , The Cloud Roadshow





