Malware trends – Part 2 ( Free Guide)
Malware trends
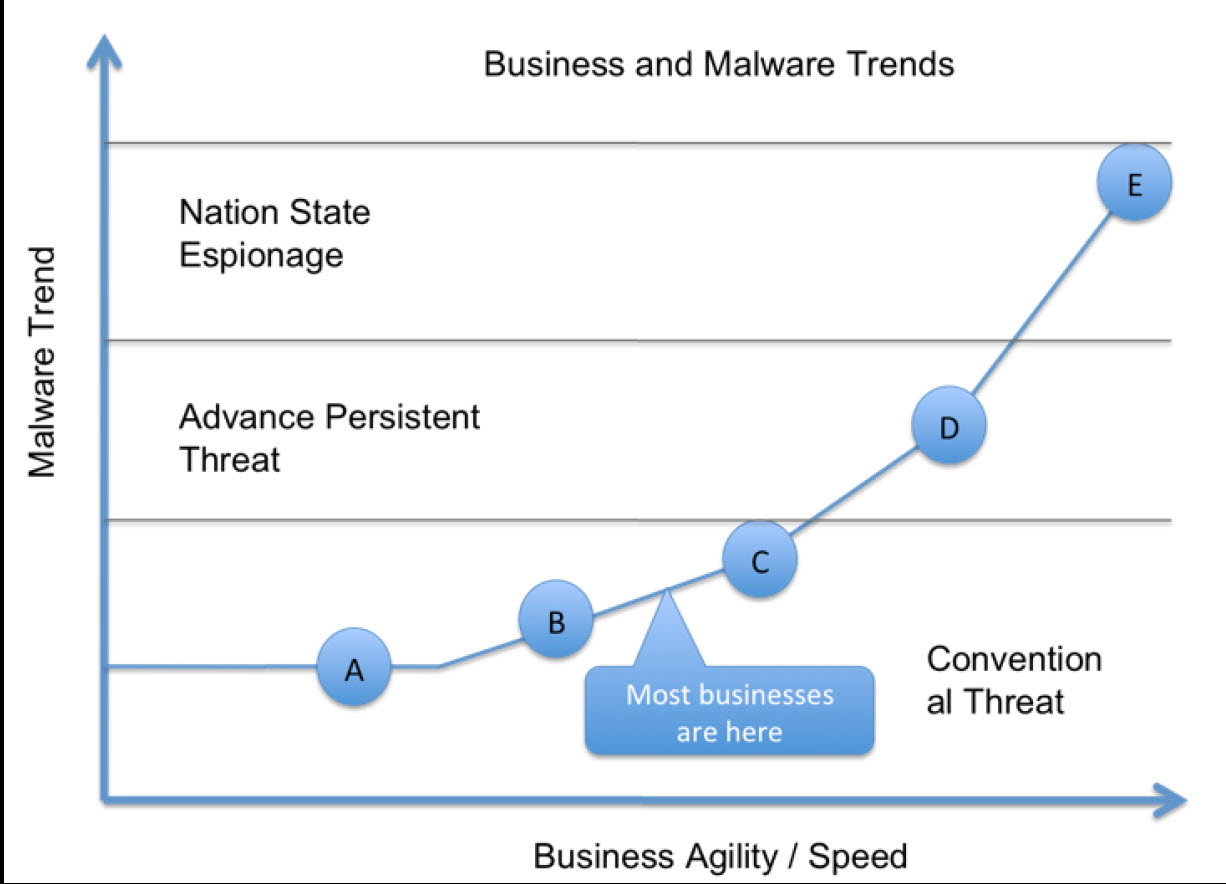
Threat actors are becoming more and more sophisticated, often making it nearly impossible for enterprises to defend against them or for end customers to identify visual indicators of compromise that could prevent the next cyber attack. Even though malware and its families are not new, there is no shortage of new payload and exploitation techniques.
On the dark web, there are countless commercial malware providers that offer a variety of malware services, such as the following:
Ransomware: The average cost ranges between $250-300.
Spyware: A simple data stealer costs approximately $10.
Remote Access Trojans: These range between $500-1,000.
ATM malware: Because a single ATM could store approximately $150,000, ATM malware remains at a high price range: $1,500-3,000.
Next to custom-made malware, ATM malware remains the most expensive malware available on the dark web. While global outbreaks such as WannaCry or NotPetya can have a serious impact on the global economy, they still represent a small fraction of the commodity malware that targets unpatched computers. Modern malware, however, has become a serious threat because traditional security solutions that rely on signatures won’t be able to respond to them.
Modern malware not only includes zero-day vulnerabilities, but also has polymorphic capabilities. Polymorphic malware is able to change its own characteristics, making it impossible to detect with an antivirus solution that purely relies on signatures. This way, threat actors are circumventing signature-based detection. According to Microsoft, 96% of malware nowadays runs once and then never runs again.
In addition to polymorphic malware, there is an ongoing increase in crypto-mining malware. This is despite the decline of the market cap for cryptocurrency. This is a result of the fact that cryptocurrency offers threat actors a way to hide while receiving the ransom from their targets.
Malware infection vectors
In the data breach report, Verizon shared an interesting perspective on the infection vectors used by threat actors with malware. This showed that 81% of all malware infections happened through a cyber attack where the malware was remotely installed or injected. The following diagram illustrates the Verizon study:

Injected by remote attacker
Threat actors leverages vulnerabilities that allow them to execute remote commands through software
Phishing and spear phishing techniques are very old forms of computer-based social engineering. Essentially, all that the threat actor needs to do is prepare a believable email with a call to action that the target will interact with, either by opening an attachment that contains a malicious document or by clicking on a hyperlink that redirects the target to a malicious website.
Auto-executed web infection
In the event of the target automatically executing a web infection, the threat actor leverages vulnerabilities on a website in order to plant their malicious payload on their target. The victim is unaware of this and simply browses a website that appears to be legitimate.
User-executed web infection
Unlike an auto-executed web infection, where the threat actor hides their malware, in the case of a user-executed web infection, the threat actor is trying to trick the victim into performing an action on the website. This may include downloading a specific file.
Installed by other malware
As part of the attack kill chain, there is the C2C phase. In this event, the threat actor has direct communication with the compromised computer. By leveraging C2C
communication, it is possible for the threat actor to also install additional malware on the compromised computer.
Network propagation
Threat actors regularly scan internet-facing IP ranges of enterprises to detect computers that are reachable. Once identified, the threat actor then proceeds with different techniques, such as brute-force attacks or vulnerability scans.
Portable media
It’s human nature to be curious and threat actors that specialize in social engineering are particularly aware of that. One of the oldest social engineering techniques is baiting. This is the process of using malicious portable media to compromise a computer. Operation Stuxnet, a state-sponsored attack against Iran suspected of being conducted by the Nation States, leveraged this technique. In this case, the threat actor will typically drop malicious portable media into locations where they’re likely to be found by the target. The expectation is that because humans are curious by nature, they will plug that portable media into their computer.
Coded into existing software
Supply chain attacks have become a serious threat. Threat actors are increasingly focusing on understanding who the suppliers and vendors of their target are and then
compromising them to get a foothold in the final target.
While many large Fortune 100 companies have a large security budget, the smaller companies that do business with these companies do not. But even the smallest company that works for a Fortune 100 company will eventually need to upload an invoice through the Fortune 100 system. Another example is compromising ISVs, which have simple tools that are leveraged by the target. Most commonly, threat actors will try to compromise their update engine.
Summary
There are many different kinds of malware. Not all malware is the same, or can be contained and stopped in the same way. In this chapter, you learned about different
malware families and how they spread. This will help you to better plan your defense strategy. The next chapter is dedicated to vulnerabilities and exploits, which are some of= the most powerful weapons that hackers can use to compromise a system and perform malicious activities.
To read part 1 : Click Here
Highlights of Part 1
The Malware Plague
Malicious software—commonly referred to as malware—is used by threat actors to perform malicious activities on a host system. These malicious activities include compromising the corporate network, identity theft, and data exfiltration. The evolution of connected devices and the fact that it has become practically impossible to run an enterprise without a computer has increased the volume of threat actors leveraging malware as part of a cyber attack.

Malware can come in the form of scripts or executable code. There are many different classes of malware, but the most well known is by far computer viruses and computer Trojans. Threat actors no longer need to find their own vulnerabilities or build their own malware. Instead, they can procure them through the dark web. There has been an increased demand for sophisticated malware that is used by state-sponsored threat actors and organized crime syndicates:
With advancements in malware development, a new risk has arisen in the form polymorphic malware. Polymorphic malware is malware that runs once and never runs
again, making it extremely difficult for antivirus providers to prevent malicious activities.
Early on, threat actors discovered the benefit of leveraging malware during cyber attacks against institutes in the financial services industry. Once malware had reached the target
endpoint, threat actors were able to illegally transfer funds from their target to accounts controlled by the threat actor. In addition to this, because ATMs are connected to the corporate network, threat actors focused on leveraging malware to attack ATMs.
Throughout this article, you will learn about malware classes and get an insight into some of the most commonly used malware families utilized as part of cyber attacks within the
financial services industry.
Malware categories
It is important to understand the different malware categories that are leveraged by threat actors during cyber attacks. Only by understanding the differences between a computer virus and a computer Trojan, for example, will you be able to build prevention capabilities.
While end users often assume that malware is only applicable to computers, it is important to understand that malware can also affect any connected device, including smartphones and industry appliances
Depending on the objective of the threat actor, the group might use a specific malware family or a combination of malware. It is recommended that security teams build their Indicators of Compromise (IOC) aligned to the cyber attack kill chain.
The attack kill chain is a process that describes how threat actors perform a cyber attack with malware. The following diagram illustrates the attack kill chain:
- Computer virus:
- Computer worm
- Ransomware
- Troja
- Rootkit
- Spyware
- Adware
- Download the Best Free Anti Virus from Comodo
For more Click Here





