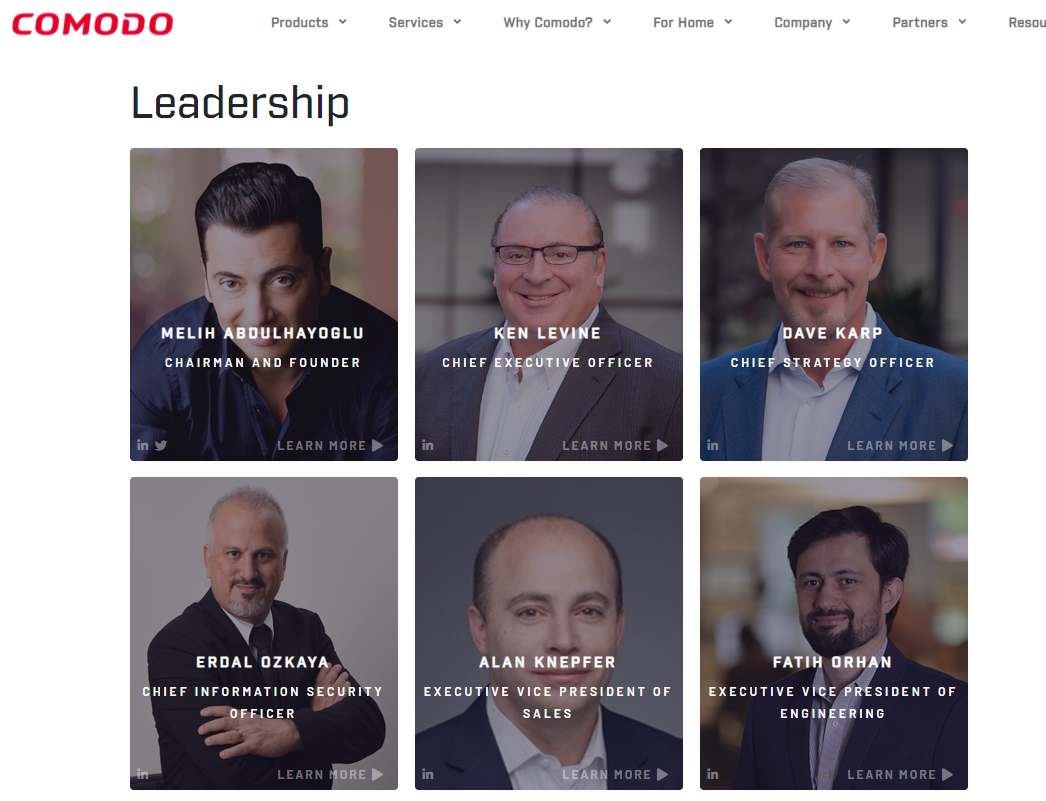
In a world where preventing all cyberattacks is impossible, Comodo delivers an innovative cybersecurity platform that renders threats useless across the LAN, web and cloud.
The Comodo Dragon platform enables customers to protect their systems and data against even military-grade threats, including zero-day attacks. It is highly effective at addressing the onslaught of ransomware. Based in Clifton, New Jersey, CSS has a 20-year history of protecting the most sensitive data for businesses and consumers globally. In 2018, CSS embarked on a journey to be the leader in endpoint security.
Today, CSS technology is precise, vigorous, and tailored to solve problems without downtime or undue stress. It renders an almost immediate verdict on the status of any unknown file to be handled accordingly by either software or human analysts. This shift from reactive to proactive makes CSS unique. It allows the capacity to protect all domains of business activity and threat—from network to web to cloud—with confidence and efficacy.
This fast and competent technology provides a seamless user experience and promotes ongoing customer trust. And, it recognizes a vital reality: while you cannot prevent 100% of malware – you can render malware useless.
Innovative Cybersecurity Solutions to Render Attacks Useless
The Problem
Some things in life are unavoidable, and malware is quickly becoming one of them. According to experts, emerging viruses, worms, Trojans, and other malicious “wares” generate approximately one million new specimens of hostile and intrusive software each day. Although many cybersecurity vendors will promise full protection against threats —the truth is, they can’t. No one can.
Businesses and people must accept that malware cannot be successfully blocked 100% of the time, nor can it be mitigated through mere defensiveness. Undetected threats are now a reality of digital age. And as such, the fight against this robust enemy will require a far more innovative and holistic approach to protection.
The Effect
Data surveys offer a glimpse into just how far down the attack cycle today’s malware has travelled, and the statistics are unsettling at best. As companies continue to zero in on the silver bullet of “protection” without considering the redundancy and impotence of their security layers, the result is a porous security posture with limited capabilities.
An attack cycle consists of four key stages:
Delivery of malware
Pre-execution
Runtime as malware attempts to execute
Post-damage remediation
While a great deal of this threat can be prevented in the first phase, the defense in depth ability to block malware execution in real time—and repair the damage—hovers around 85%. This number simply isn’t high enough to beat the greatest enemy to the world of computing.
The Comodo Cybersecurity Solution
As a leader in cybersecurity for over twenty years, Comodo Cybersecurity seeks to protect businesses by understanding the true nature of the digital environment and what malware needs to survive. Without unfettered access and the ability to execute its malicious program, it has no power to breach other systems. But malware does have the capability to penetrate initial security measures, which means it cannot be fully prevented or denied—instead, it must be mitigated through the acceptance of its ability to penetrate even the most well-guarded systems.
While Comodo Cybersecurity solutions offer comprehensive detection services, our real prowess comes from the ability to determine if unknown files entering the system are good or bad, with no sandbox lag time or delayed productivity.